A newly discovered vulnerability in Ubuntu Desktop allows locally logged-in users with limited privileges to gain full root access.
Security researchers at the Qualys Threat Research Unit (TRU) have identified a high-severity vulnerability in Ubuntu Desktop that allows attackers with local user rights to gain full control over an affected system. Tracked as CVE-2026-3888, the flaw affects standard installations of Ubuntu Desktop 24.04 and later and has been rated “high” with a CVSS score of 7.8.
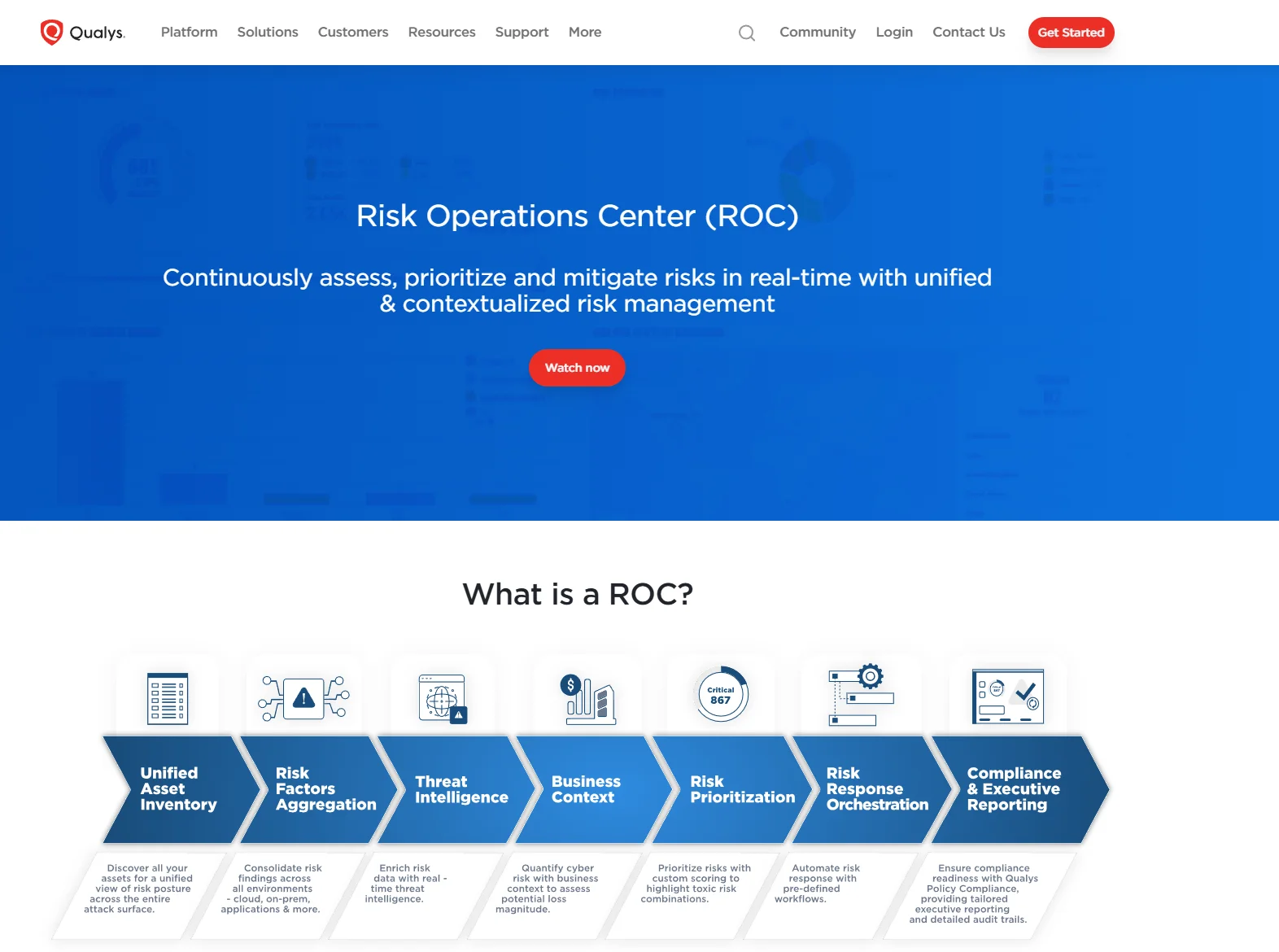
What makes this vulnerability particularly notable is its origin: it does not stem from a single programming error but from an unintended interaction between two core system components. The affected components are snap-confine, which sets up the sandbox environment for Snap applications with elevated privileges, and systemd-tmpfiles, which handles the automated cleanup of temporary directories. Only the combination of both components creates the exploitable attack surface.
The attack follows a multi-stage pattern that requires a degree of patience. Over a period of days or weeks – depending on system configuration – systemd-tmpfiles deletes a directory required by snap-confine. An attacker with local access can then recreate this directory with manipulated contents. The next time a user launches a Snap application, snap-confine processes this data with root privileges, executing arbitrary code with maximum system rights.
Although the timing requirement makes this attack more technically demanding than typical instant exploits, the damage potential remains significant. Full root access means an attacker can manipulate system files, install backdoors, read sensitive data, and circumvent all operating system protections. In enterprise environments with multiple local users – such as shared workstations or development machines – the risk is particularly relevant.
The discovery highlights a structural issue in modern Linux environments: the growing modularity introduced by technologies such as Snap, systemd, or containerized architectures creates attack surfaces that only emerge from the interplay of individual components. Traditional security audits that examine components in isolation do not reliably detect such interactions. Permission boundaries and automated system processes can interact in ways that were never anticipated during the original design of either component.
During their analysis, researchers also identified a second vulnerability in a pre-release version of Ubuntu 25.10. A race condition in the rm command of the Rust-based uutils coreutils could have allowed attackers to manipulate file operations within privileged cron jobs. This flaw was addressed before release, in part by reverting to the established GNU coreutils implementation. The incident demonstrates that well-intentioned modernization efforts – such as replacing classic C tools with Rust alternatives – can introduce new attack vectors if not rigorously evaluated.
For Ubuntu users and administrators, the recommended course of action is straightforward: available patches for the snapd package should be applied promptly. Updated packages are available through standard Ubuntu package repositories. Systems where an immediate update is not feasible should be monitored closely for unauthorized local access until the fix is in place.
CVE-2026-3888 is another reminder that local privilege escalation remains a central risk in modern operating system environments, despite improved security architectures. The complexity of today’s systems – with their numerous dependencies, automated processes, and modular designs – increases the likelihood that security-relevant interactions between components go unnoticed. Regular patch cycles and a thorough understanding of system component interactions therefore remain indispensable.

Dr. Jakob Jung is Editor-in-Chief of Security Storage and Channel Germany. He has been working in IT journalism for more than 20 years. His career includes Computer Reseller News, Heise Resale, Informationweek, Techtarget (storage and data center) and ChannelBiz. He also freelances for numerous IT publications, including Computerwoche, Channelpartner, IT-Business, Storage-Insider and ZDnet. His main topics are channel, storage, security, data center, ERP and CRM.
Contact via Mail: jakob.jung@security-storage-und-channel-germany.de